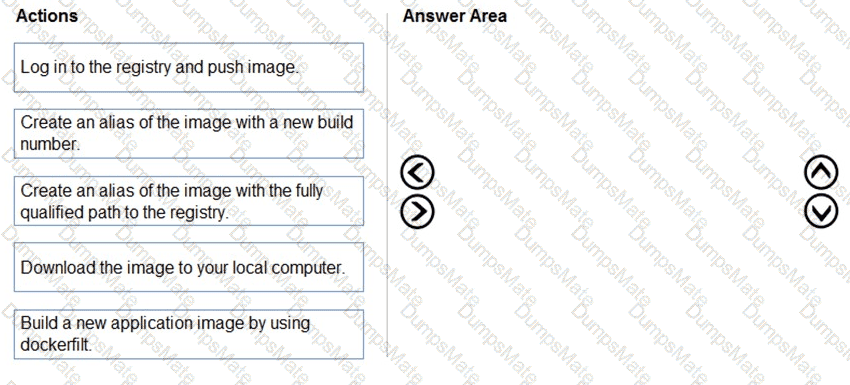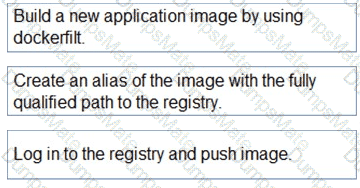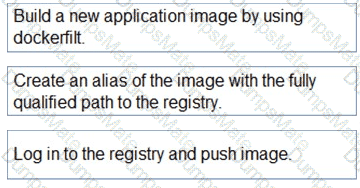
Step 1: Build a new application image by using dockerfile
Step 2: Create an alias if the image with the fully qualified path to the registry
Before you can push the image to a private registry, you’ve to ensure a proper image name. This can be achieved using the docker tag command. For demonstration purpose, we’ll use Docker’s hello world image, rename it and push it to ACR.
# pulls hello-world from the public docker hub
$ docker pull hello-world
# tag the image in order to be able to push it to a private registry
$ docker tag hello-word < REGISTRY_NAME > /hello-world
# push the image
$ docker push < REGISTRY_NAME > /hello-world
Step 3: Log in to the registry and push image
In order to push images to the newly created ACR instance, you need to login to ACR form the Docker CLI. Once logged in, you can push any existing docker image to your ACR instance.
Scenario:
Coho Winery plans to move the application to Azure and continue to support label creation.
LabelMaker app
Azure Monitor Container Health must be used to monitor the performance of workloads that are deployed to Kubernetes environments and hosted on Azure Kubernetes Service (AKS).
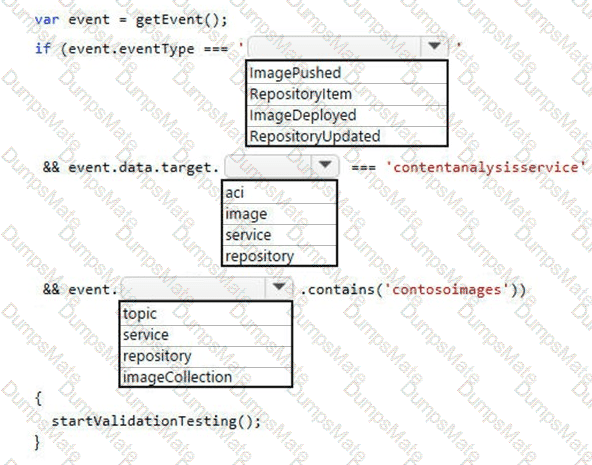
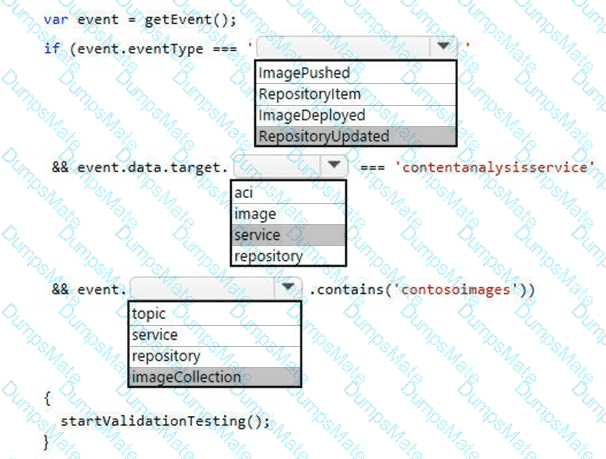
You must use Azure Container Registry to publish images that support the AKS deployment.
[Reference:, https://thorsten-hans.com/how-to-use-a-private-azure-container-registry-with-kubernetes-9b86e67b93b6, , https://docs.microsoft.com/en-us/azure/container-registry/container-registry-tutorial-quick-task, , , , ]