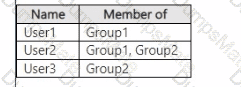
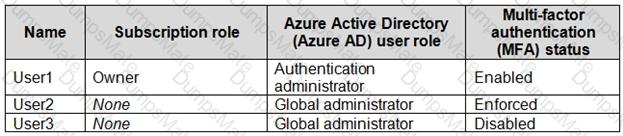
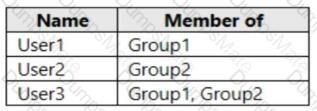
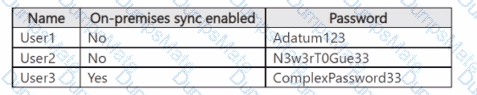
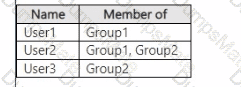
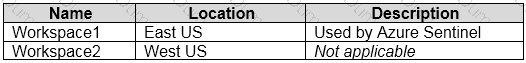
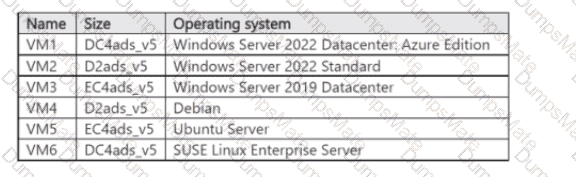
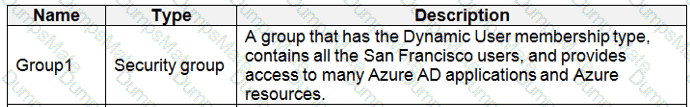
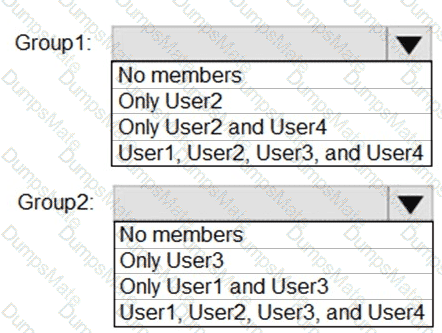
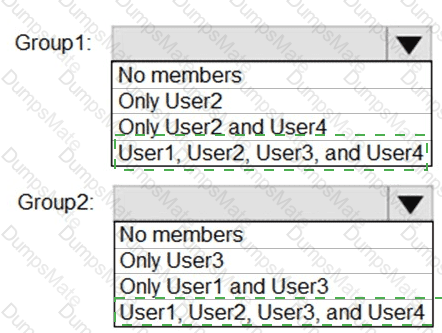
You have a Microsoft Entra tenant that contains the users shown in the following table.
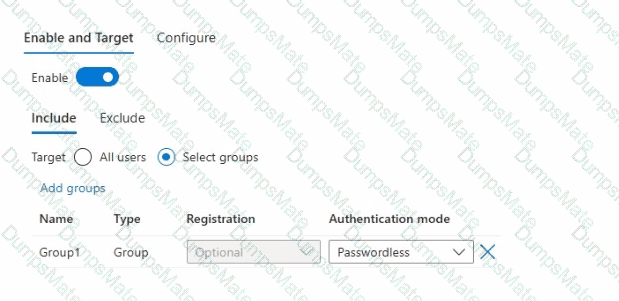
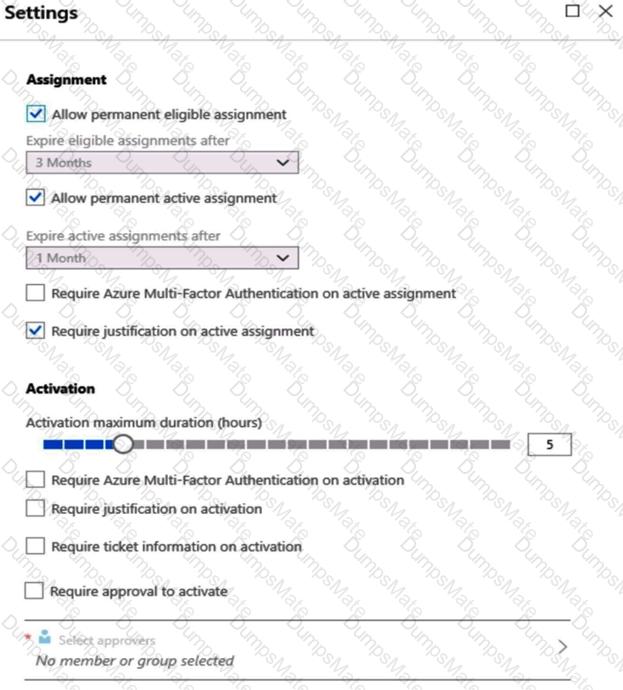
You configure a Conditional Access policy that has the following settings:
• Name: CAPolicy1
• Assignments
o Users or workload identities: Group1
o Target resources: All cloud apps
• Access controls
o Grant access: Require multifactor authentication
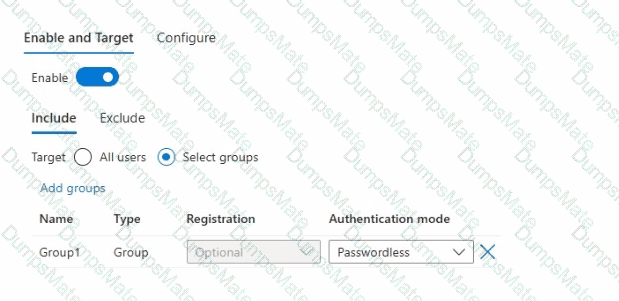
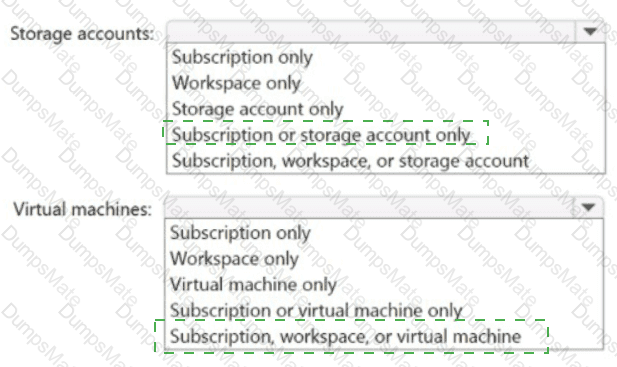
From Microsoft Authenticator settings for the tenant, the Enable and Target settings are configured as shown in the Enable and Target exhibit. (Click the Enable and Target tab.)
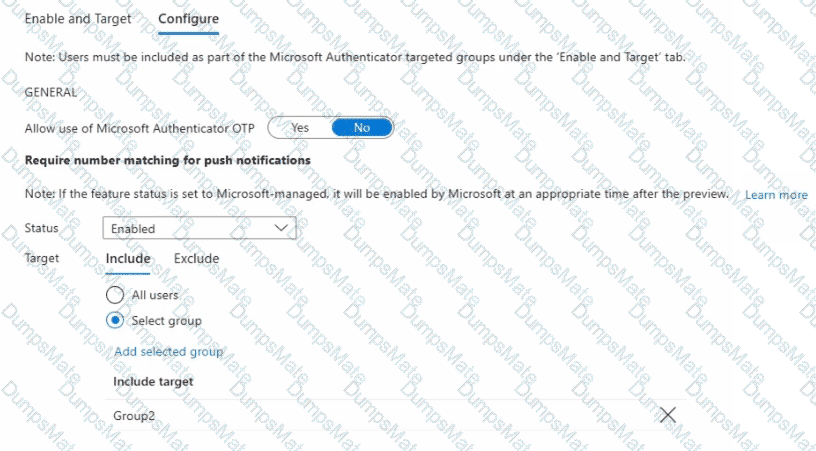
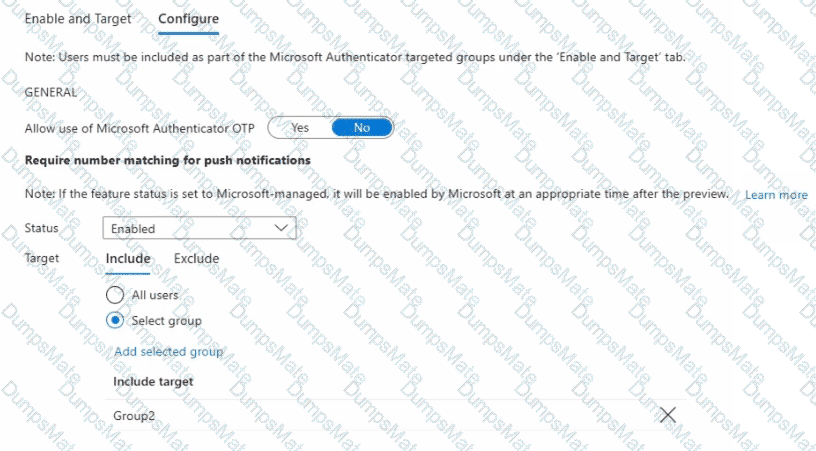
From Microsoft Authenticator settings for the tenant, the Configure settings are configured as shown in the Configure exhibit. (Click the Configure tab.)
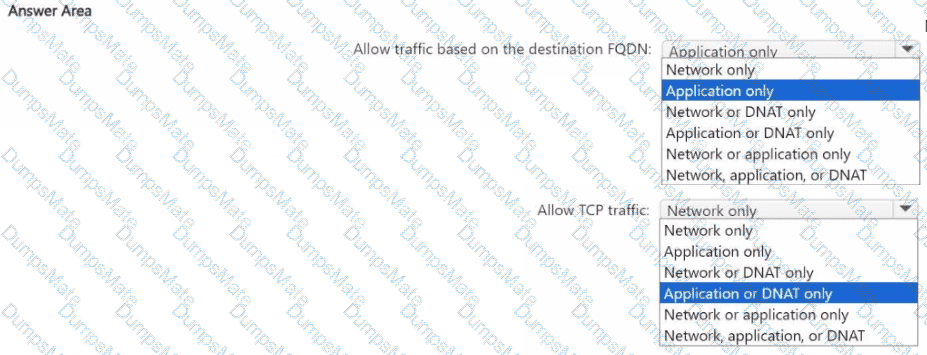
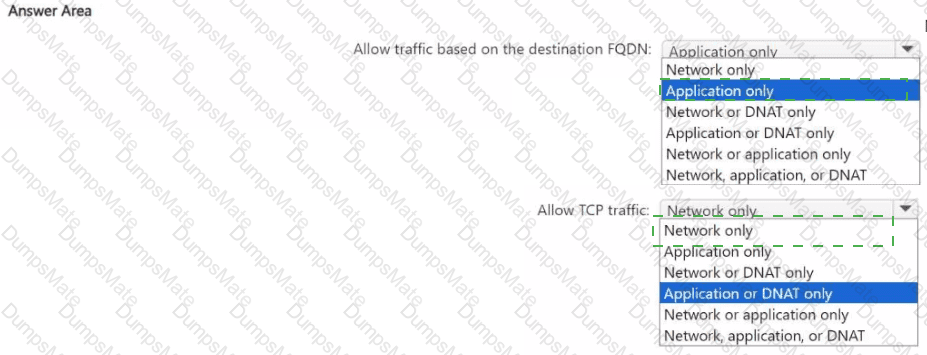
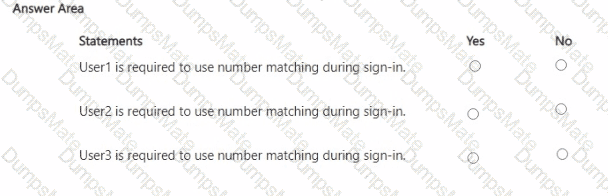
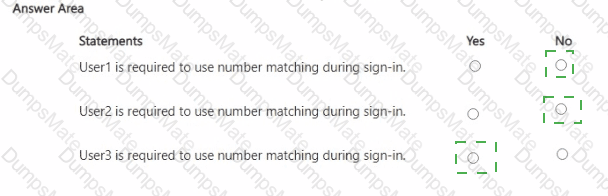
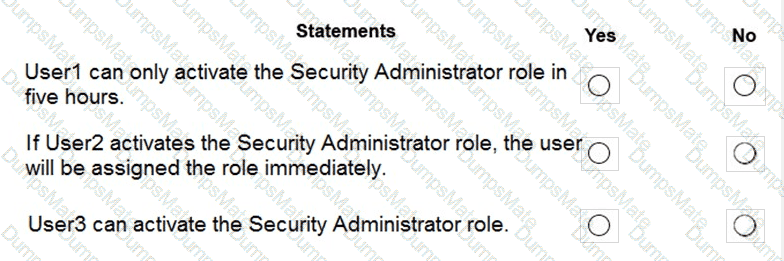
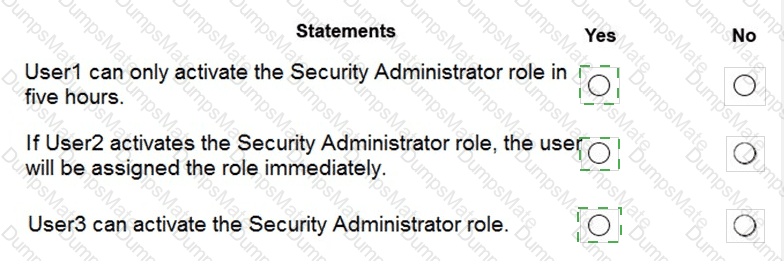
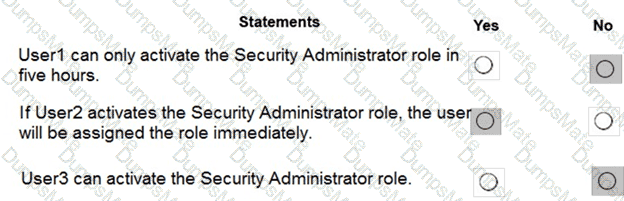
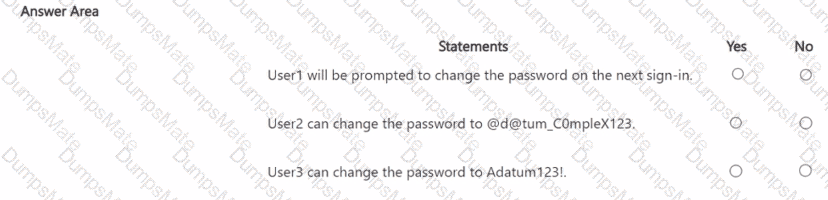
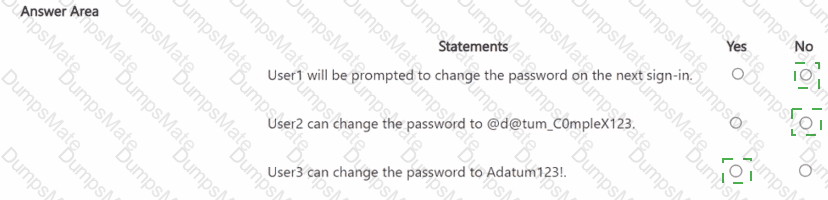
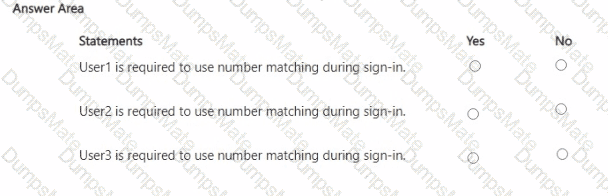
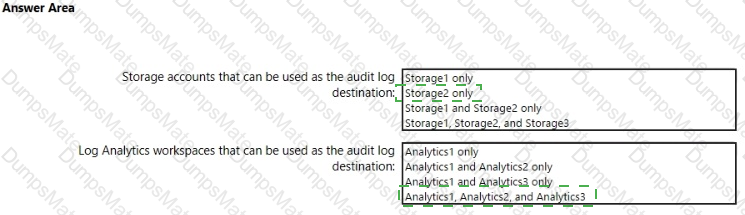
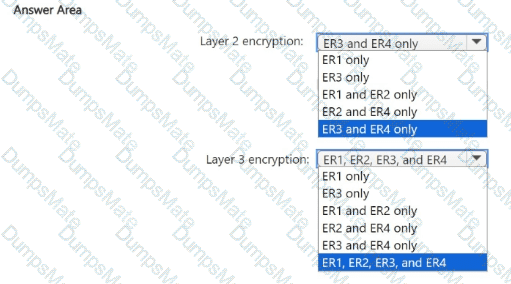
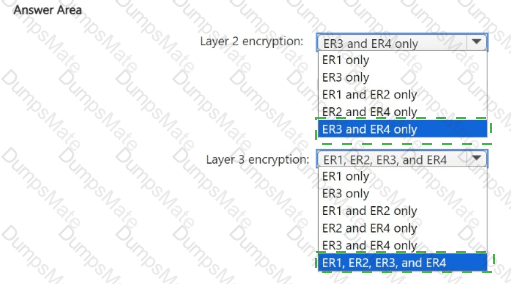
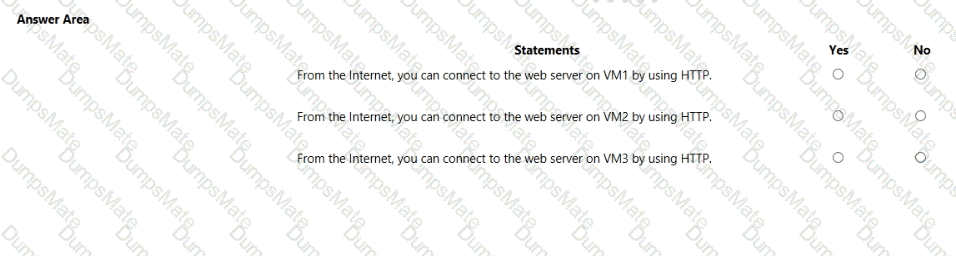
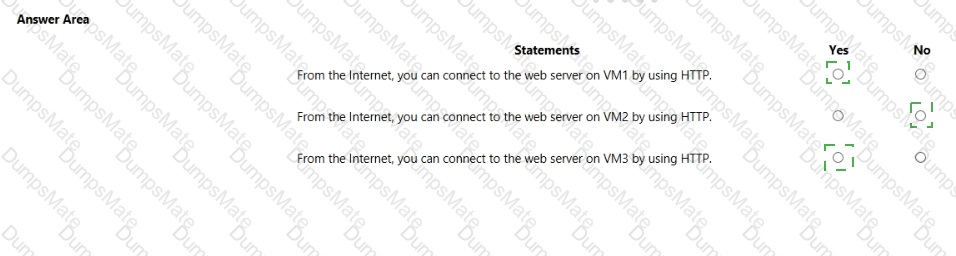
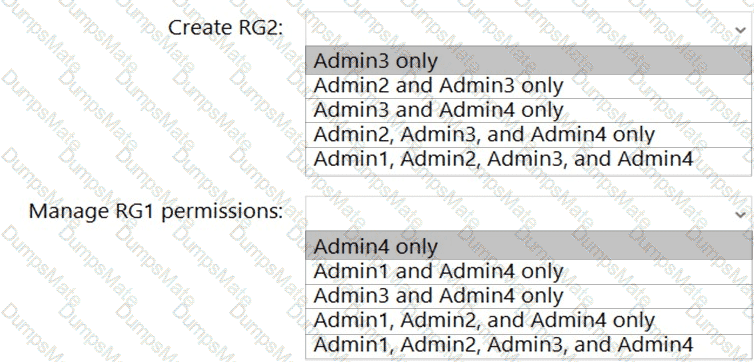
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.



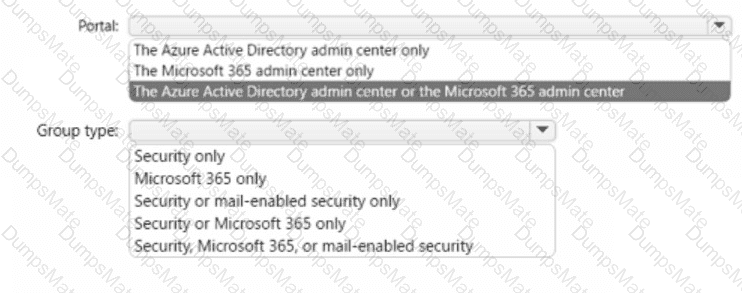
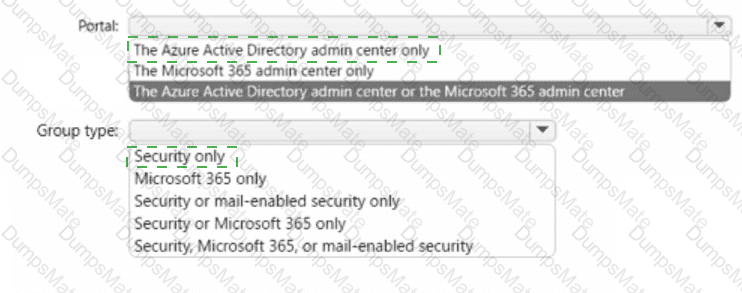
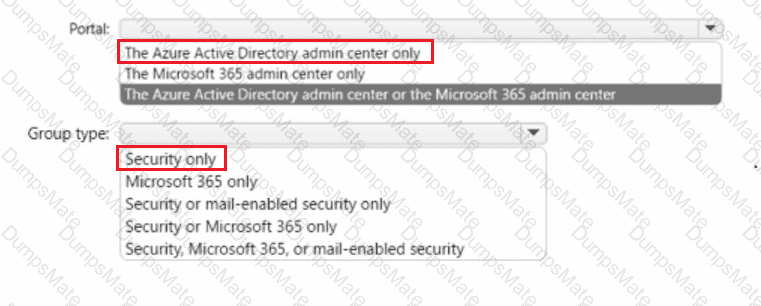
 Graphical user interface, text, application, chat or text message Description automatically generated
Graphical user interface, text, application, chat or text message Description automatically generated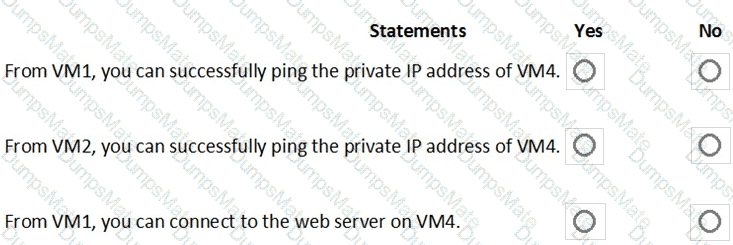
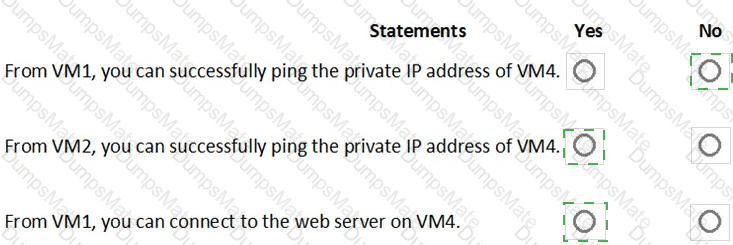
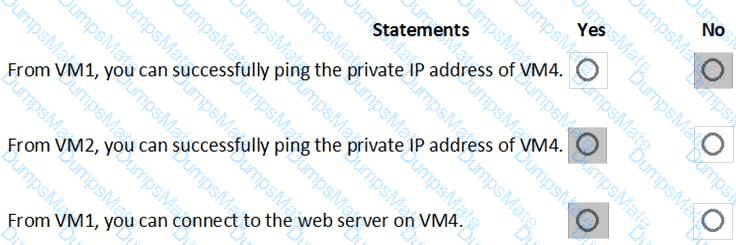
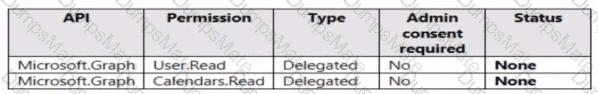
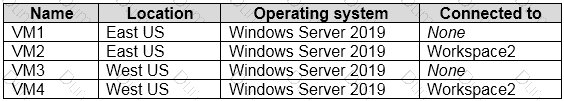
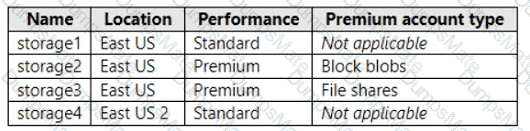
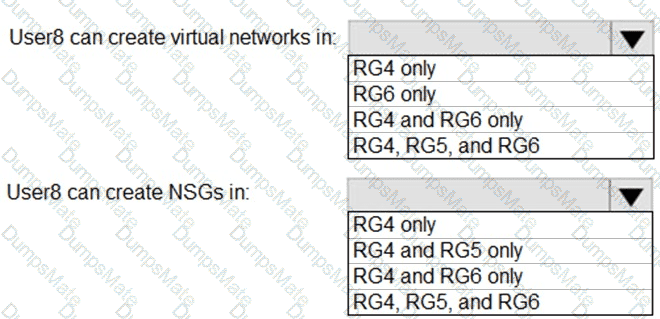
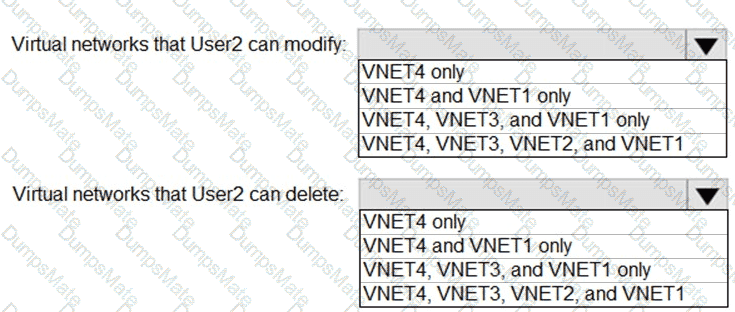
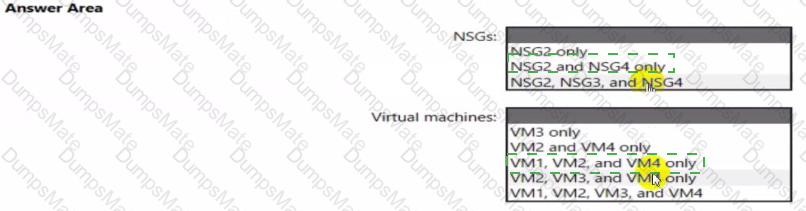
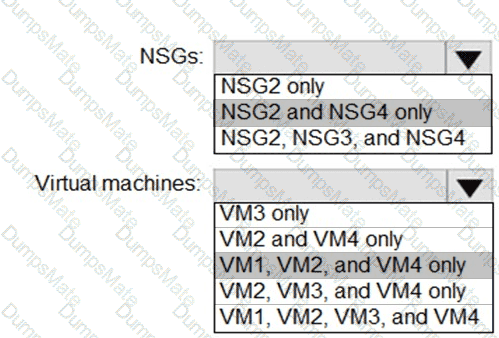
 Table Description automatically generated with medium confidence
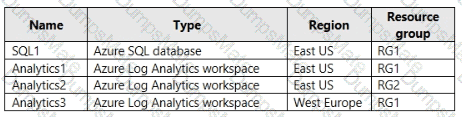
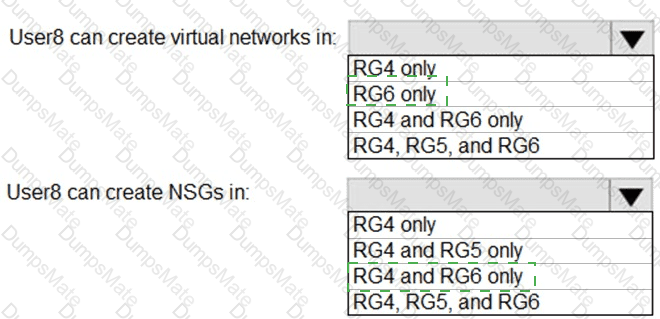
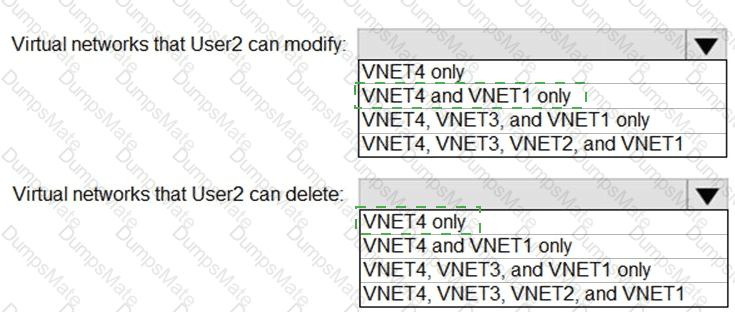
Table Description automatically generated with medium confidence
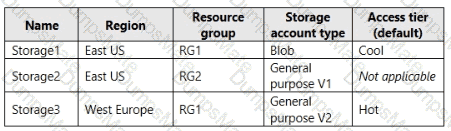
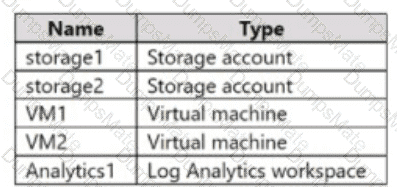
 Table Description automatically generated
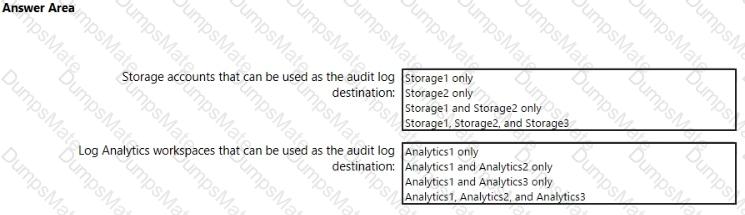
Table Description automatically generated
 Graphical user interface, text, application, chat or text message Description automatically generated
Graphical user interface, text, application, chat or text message Description automatically generated