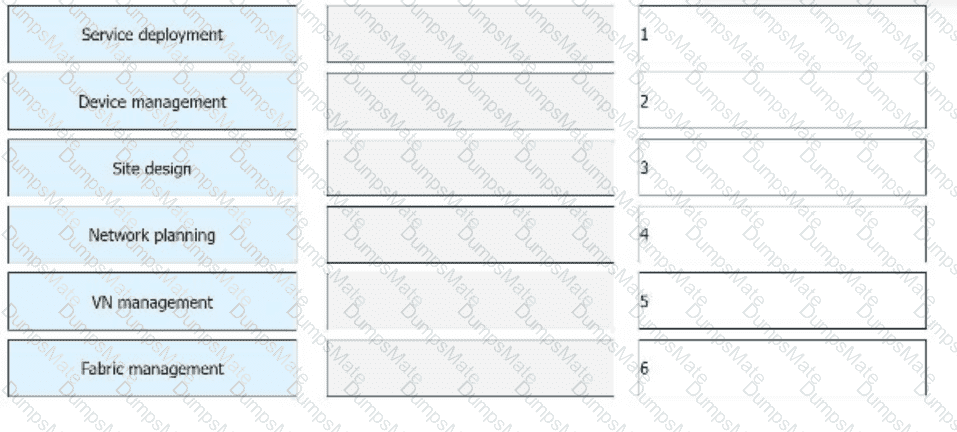
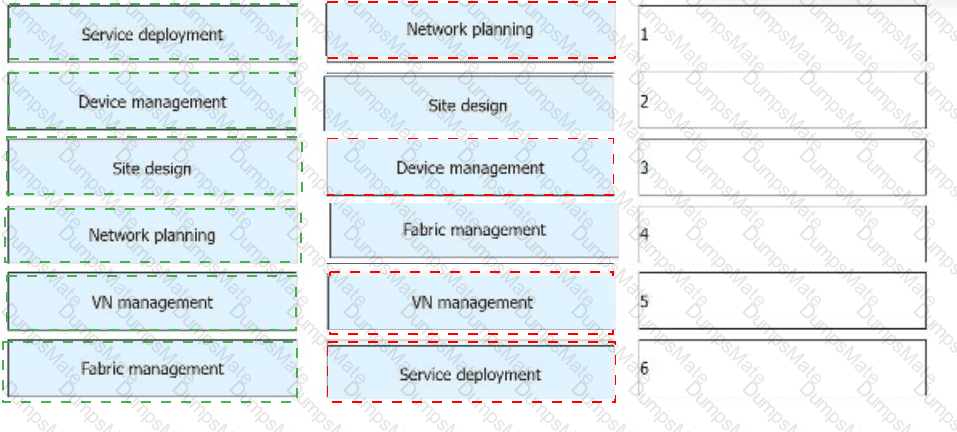
Correct Order of Steps:
1️⃣ Network planning
2️⃣ Site design
3️⃣ Device management
4️⃣ Fabric management
5️⃣ VN (Virtual Network) management
6️⃣ Service deployment
Understanding the iMaster NCE-Campus Deployment Process
???? iMaster NCE-Campus is Huawei’s AI-driven network automation and management platform for campus networks.
???? The deployment follows a structured sequence to ensure a fully operational network.
Detailed Explanation of Each Step:
✅ 1️⃣ Network Planning (First Step)
Defines the overall network architecture, topology, and business requirements.
Determines WAN, LAN, and WLAN coverage for the campus.
Ensures IP addressing, VLANs, and security policies are planned.
✅ 2️⃣ Site Design (Second Step)
Creates site layouts and determines device placement (switches, APs, routers).
Defines power, cabling, and uplink requirements for optimal connectivity.
✅ 3️⃣ Device Management (Third Step)
Onboards network devices (e.g., switches, APs, firewalls) into iMaster NCE-Campus.
Configures initial settings such as IP addresses, interfaces, and SNMP settings.
Ensures devices are registered and reachable in the management platform.
✅ 4️⃣ Fabric Management (Fourth Step)
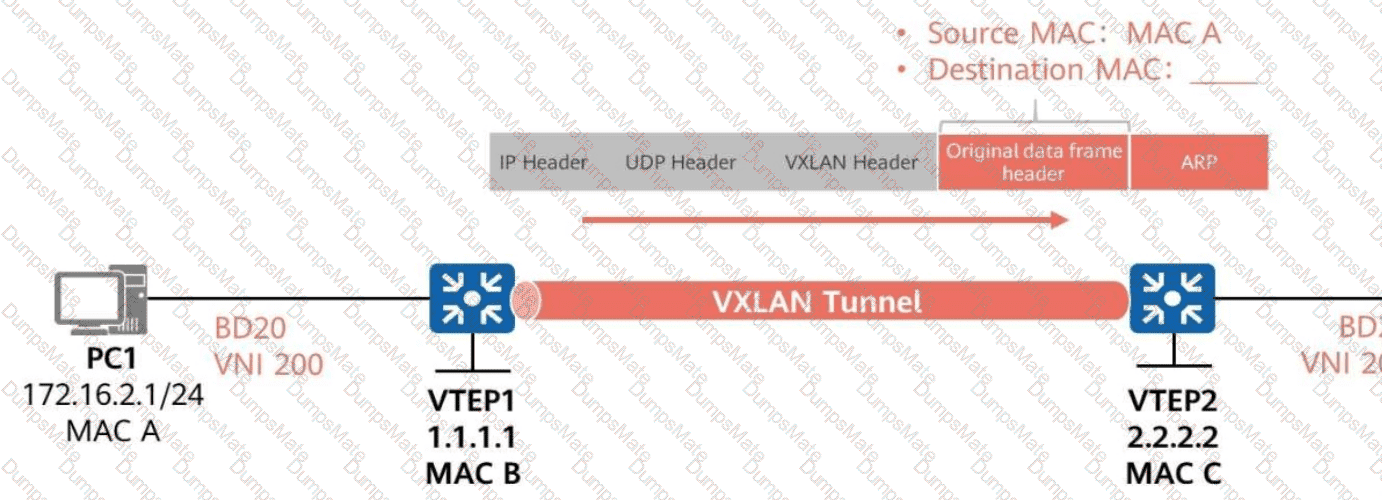
Establishes VXLAN-based network fabric for automated Layer 2/3 connectivity.
Configures EVPN/VXLAN overlays, VTEPs, and underlay routing.
✅ 5️⃣ VN (Virtual Network) Management (Fifth Step)
Defines virtual networks (VNs) for different departments, tenants, or services.
Configures QoS, ACLs, and network segmentation policies.
✅ 6️⃣ Service Deployment (Final Step)
Activates network services like DHCP, security policies, and application access.
Ensures that end-user connectivity and application traffic policies are in place.
Why Is This the Correct Order?
✅ Each step builds upon the previous one, ensuring a smooth and structured deployment process.
✅ Service deployment comes last because it finalizes user access and application connectivity.
Real-World Application:
Enterprise Campus Networks: Deploys secure, scalable campus connectivity with AI-based automation.
University Campuses & Smart Cities: Uses SDN-driven network segmentation and automation to simplify operations.
✅ Reference: Huawei HCIE-Datacom Guide – iMaster NCE-Campus Deployment & Automation