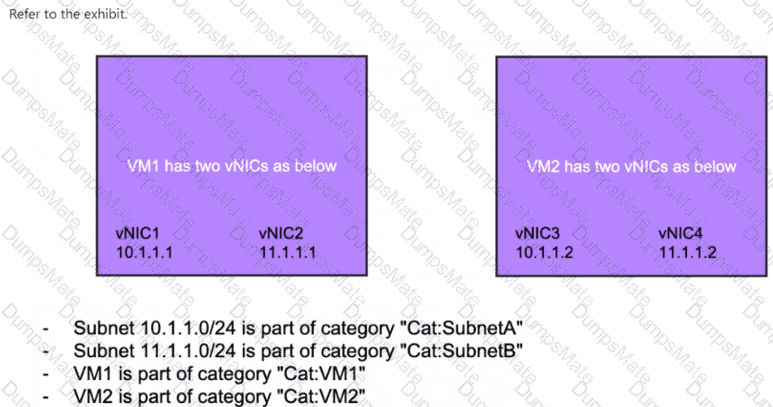
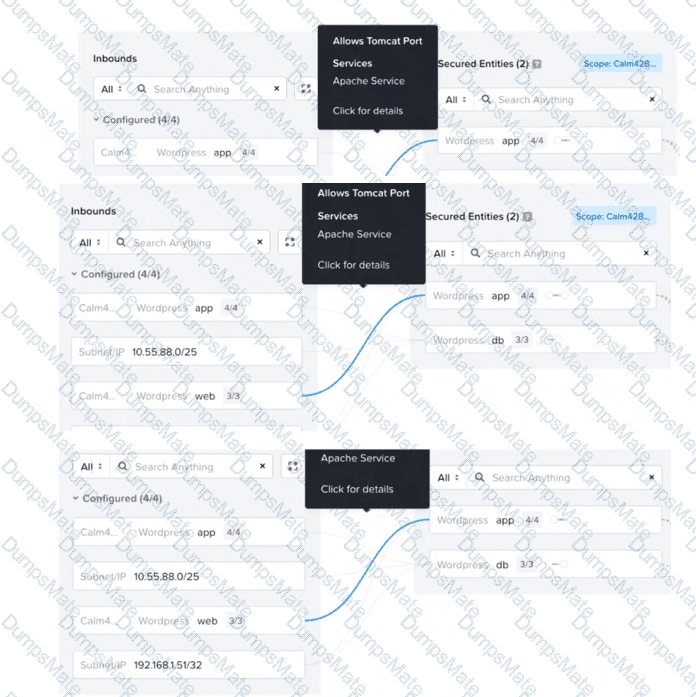
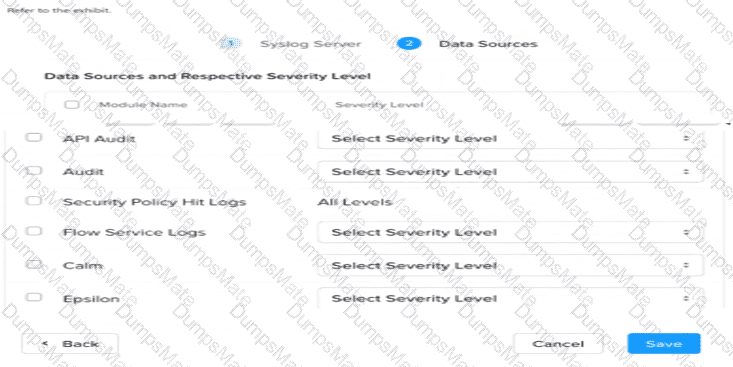
An administrator uses Nutanix Flow to secure a three-tier application (Web, App, and Database tiers). After observing the traffic, they find that: The Web tier communicates with the App tier over HTTP (port 80) The App tier communicates with the Database tier over TCP port 1433 The Database tier does not initiate connections The Web tier receives inbound HTTP traffic from the corporate DMZ on port 8080 No other traffic should be allowed What should the administrator do to document and then securely apply these flows in Nutanix Flow?